If you are pretty familiar with Java development, this post will seem silly to you. But I’m not. Many times, you can learn a lot from failures as well, so this one I’d like to document.
Basically, I had gotten a command prompt as a lower privileged user on a machine. I was looking to get administrator access somehow, and I noticed that Java 7 Update 4 was running, which is vulnerable to CVE-2012-4681. You always hear of this one as a “privilege escalation” exploit, so I thought by popping out of the Java sandbox, you’d also pop out as an administrative user.
News flash. It doesn’t work that way. The exploit works, but you pop out of the sandbox as the same user as you ran the command.
I’m going to explain how to do it anyway. Those Java developers can stop here, but the rest of us might still learn something.
What do I start out with?
Most exploits are captured via twitter, or some sort of pastebin website. Usually with twitter linking to a pastebin, which is the case here. The source code was tweeted by @jduck1337 pointing to pastie.org/4594319. Grab the source code from there because that’s what we’re going to start out with.
Also, don’t forget to install a vulnerable version of Java. Any Java 7 version at revision 7 or below should work.
I have my code, now what do I do with it?
You can see the class is called Gondvv. So you’ll need to save that file as Gondvv.java. Then erase that first line that says: package cve2012xxxx; This will be a standalone file, not a package.
You’ll notice a bunch of jibberish, but near the end of the file you’ll see the purpose is simply to open calc.exe. So no worries – the code as it stands is not actually malicious.
Finally, compile your code. Go to the command prompt, browse to where your Gondvv.java file is, and type the following:
javac Gondvv.java
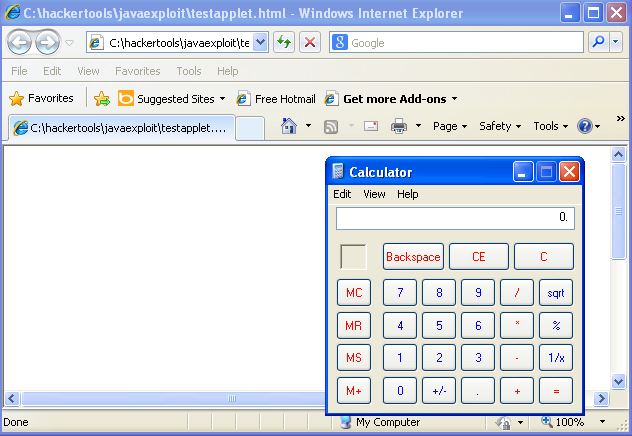
That was easy. This should have created a Gondvv.class file. Now since this was originally meant to run as a Java applet, you’ll need to create an HTML file with the following source:
<applet align=”center” code=”Gondvv.class” width=”800″ height=”500″></applet>
That alone will do it. Run your HTML file, and your calculator will pop up. Congrats, you successfully exploited the vulnerability!
How about privilege escalation?
The next step was to make this a command line prompt. Remember, I had command line as a lower privileged user already. I was hoping to run commands inside this program to be higher privileged. So the next step was to strip away all the Java applet stuff.
So strip away the java.applet.Applet and java.awt.Graphics import lines. Also make it so the public class Gondvv doesn’t extend Applet. Then all the classes need to get the “static” keyword added to them. Remove the very last paint class. Finally, the public void init() class needs to be renamed to public static void main(String[] args). The end result looks like the following:
(looked terrible here. Pasted it on pastebin)
Then compile it the same as before, and run it with:
java Gondvv
Calculator should pop up! Not so exciting, but you can see it is working. In order to see who is actually running it, you can just have it run “whoami.exe” or something along those lines. Had it actually worked, I would have made it run a netcat listener or a meterpreter payload or something.
What if I just want a .jar file?
Don’t want to use the java keyword before running your file? Make a .jar file. You’ll first need to create a manifest.txt file. The contents should be as follows:
Main-Class: Gondvv
Then at the command line, simply type the following to create your .jar file:
jar cvfm javahack.jar manifest.txt *.class
Bingo, now you can just run the jar file. Enough Java for one day.