You can get a surprising amount of information from a Windows machine if it has port 445 open, especially if you happen to have a working user account on the machine (such as an account credential grabbed from another machine on the same domain).
Setup Your Testbed
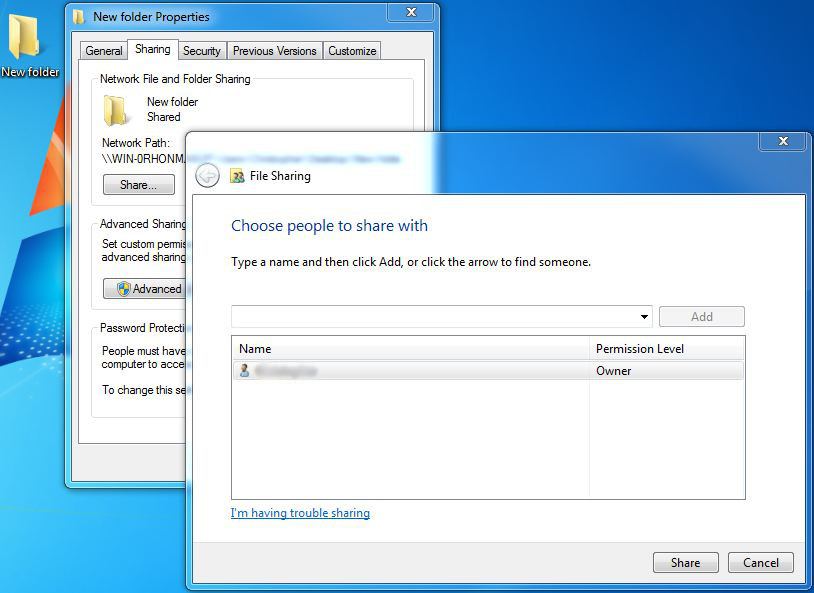
All you need to do is take any Windows host, and share something. For example, create a new folder on the desktop. Then right click on that folder, and click Properties. There is a Sharing tab.
Make sure you have also created a user with a password on this machine.
Attack
How do you find a vulnerable host?
Any Windows host with file sharing will do. These hosts are usually pretty obvious when running a nmap port scan. Ports 135, 139, and 445 will most often be open.
How do you attack that host?
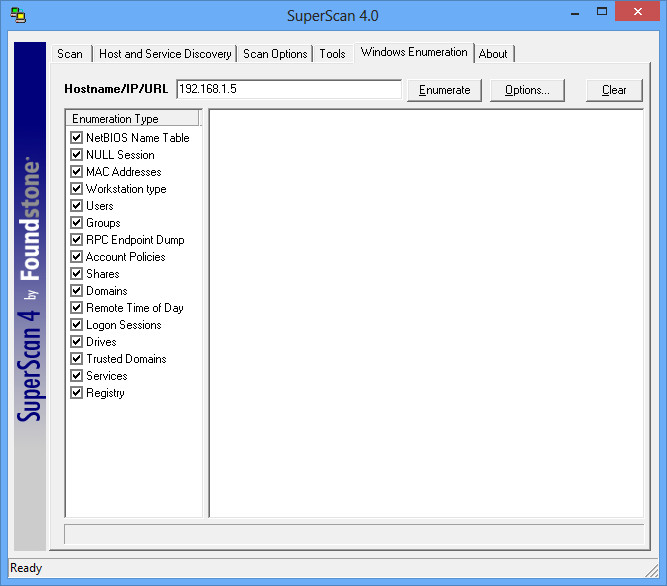
There are a number of tools and metasploit modules that do smb enumeration (try out auxiliary/scanner/smb/smb_lookupsid). However, there is an older tool that seems to work the best called superscan. It still works fine on all modern Windows operating systems, but you need to run it as an Administrator (right click, run as administrator).
Superscan gives you a number of tabs with tools (lets be honest – these other tools aren’t all that useful), but we’re going to look at the Windows Enumeration tab. Simply type in the IP of the machine you setup, and click Enumerate.
It’ll run all the modules, and most likely it’ll come back only with information on the NULL session connection and the RPC services. However if you can run an authenticated scan, it is a gold mine of information. Click on Options and enter your credentials and run the scan again.
Now you’ve got all sorts of information on the remote system, including all the groups (who are the administrative users? very useful), usernames, other shares available, uptime, account policies, who logged in last, etc. This is great, especially when you can’t access this information through RDP or anything else.